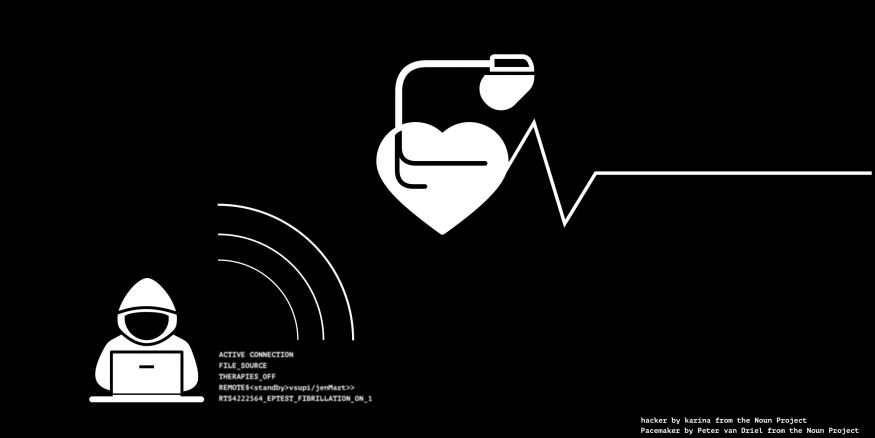
With one line of code “RTS42256H_EPTEST_FIBRILLATION_ON_1.0,” the Vice President of the United States began to feel crushing chest pain and difficulty breathing. His defibrillator, designed to save his life was doing exactly the opposite. Nicholas Brody proclaims “You still don't get it, do you? I'm killing you(1)." TV shows often draw inspiration from real life, and yet again cybersecurity in healthcare creates a compelling and irresistible plotline. In this instance, Homeland episode “Broken Hearts” depicts the Vice President of the United States having an induced heart attack after a hacker gains access to his pacemaker(1). While initially panned by media critics due to lack of plausibility, the show makers revealed that this storyline was based on real life concerns regarding Vice President Dick Cheney’s implanted cardiac defibrillator, which was replaced with a modified device in 2007 to prevent possible device tampering(2). In a CNN interview with Sanja Gupta, Vice President Dick Cheney and Cheney’s cardiologist, Dr. Jonathan Reiner, Dr. Reiner voiced to Cheney, “It seemed to me to be a bad idea for the Vice President of the United States to have a device that [...] somebody might be able to hack into. I worried that someone could kill you(2)." Despite the very real threats that exist, to date, there have been no recorded instances of patient harm from implanted medical device tampering, that we know of. However, with the increasing utilization of connected medical devices, such as pacemakers, cardiac defibrillators, insulin and other infusion pumps, there has also been an increasing concern among security researchers (also known as “white hats” or “good hackers”) and other experts regarding the ability of these devices to be commandeered by outside malicious sources.
Oversight and regulation for the cybersecurity of medical devices fall under the US Food and Drug Administration (FDA), and in recent years, the FDA has worked closely with device manufacturers and the healthcare industry to reduce potential risks through premarket (2018) and postmarket (2016) guidance on cybersecurity of medical devices(3,4). In a 2011 transcript with Deputy Director of the FDA’s Center for Devices and Radiological Health (CDRH) Bill Sutton, he states “The CDRH mission is to assure that all medical devices [...] are reasonably safe and effective [...] by looking at the benefit/risk, when we review these medical device applications(5)." However, in spite of well-tested safety protocols and FDA guidance, security researchers have been able to hack into numerous medical devices. For instance, security researcher Jay Radcliffe, a type I diabetic himself, demonstrated at Black Hat USA Security Conference in 2011, that he was able to successfully hack into his implantable insulin pump and program it to deliver a lethal dose of insulin(6). One year later, security researchers demonstrated the ability to send lethal shocks to a patient via a commandeered pacemaker as well as to administer fatal doses of a drug to a patient through hacking into a drug infusion pump(6).
Consequently, in 2013, the FDA began ramping up its cybersecurity protocols to address these gaping security issues with their approved medical devices and, even more recently, companies have paired up with security researchers to test their products(7). In 2019 at Def Con, a yearly conference for hacking and cybersecurity issues held in Las Vegas, a cybersecurity expert named Beau Woods organized a virtual playground for hackers, called the Medical Device Lab(7). This involved setting up a hospital replica including hospital rooms, a lab for bloodwork and neonatal and intensive care units where hackers would attempt to test security measures of medical technology(7). These types of hacking events have helped to establish new methods for protecting against potential threats.
As members of the healthcare sector, it is important that our patients are aware and fully informed of the possible safety concerns, regarding the cybersecurity holes produced by having a lifesaving medical device connected to a wireless network. The FDA has stringent measures in place over what is put out into the public, but there is still always room for technological improvement and concern about what is put into our bodies. However, this should not serve to undermine the importance of these devices. Instead, it should serve to create a sense of caution and inspire more active involvement with device security measures to ensure that Homeland’s storyline does not indeed become a reality for anyone. In the upcoming weeks, further elaboration will be given on cybersecurity attacks, theft of patient information and how it's being sold on the “dark web”.
References:
- Zuckerman, Esther. (2012, Dec. 3). Just How Impossible Was Last Night’s Homeland? Retrieved from https://www.theatlantic.com/culture/archive/2012/12/just-how-impossible-was-last-nights-homeland-episode/320910/.
- Ford, Dana. (2013, Oct. 24). Cheney’s Defibrillator Was Modified to Prevent Hacking. Retrieved from https://www.cnn.com/2013/10/20/us/dick-cheney-gupta-interview/index.html.
- U.S. Food & Drug Administration. (2018, Oct. 18). Content of Premarket Submissions for Management of Cybersecurity in Medical Devices. Retrieved from https://www.fda.gov/regulatory-information/search-fda-guidance-documents/content-premarket-submissions-management-cybersecurity-medical-devices.
- U.S. Food & Drug Administration. (2016, Dec. 28). Postmarket Management of Cybersecurity in Medical Devices. Retrieved from https://www.fda.gov/regulatory-information/search-fda-guidance-documents/postmarket-management-cybersecurity-medical-devices.
- Sutton, Bill. (2018, Jan. 4). Overview of Regulatory Requirements: Medical Devices – Transcript. Retrieved from https://www.fda.gov/training-and-continuing-education/cdrh-learn/overview-regulatory-requirements-medical-devices-transcript.
- Jaret, Peter. (2018, Nov. 12). Exposing Vulnerabilities: How Hackers Could Target Your Medical Devices. Retrieved from https://www.aamc.org/news-insights/exposing-vulnerabilities-how-hackers-could-target-your-medical-devices.
- Marks, Joseph. (2019, Aug. 8). The Cybersecurity 202: Hackers Are Going After Medical Devices – and Manufacturers Are Helping Them. Retrieved from https://www.washingtonpost.com/news/powerpost/paloma/the-cybersecurity-202/2019/08/08/the-cybersecurity-202-hackers-are-going-after-medical-devices-and-manufacturers-are-helping-them/5d4b556088e0fa4cc4c23465/.

Justin Hull is a research fellow for Urgent Matters. A graduate in neuroscience from George Mason University. He is a medical scribe at George Washington Hospital while studying to get into medical school and has also scribed at Inova Fairfax Hospital ED.

Jordan Selzer, M.D.
Jordan Selzer is a Disaster and Operational Medicine Fellow and Emergency Medicine Physician at George Washington University. His areas of focus include operationally focused disaster response work as well as healthcare cybersecurity. He has significant disaster response experience: having worked in the US Virgin Islands after Hurricanes Irma and Maria as well as the Bahamas after Hurricane Dorian. His cybersecurity work has included collaborating with FDA regulators, FBI cybersecurity experts, and medical device security researchers. He is also a co-founder of an app-based medical tech startup MayJuun, focused on improving physician experience of healthcare delivery.
Dr. Selzer attended medical school at Loyola University Chicago and completed his residency in Emergency Medicine at Maricopa Medical Center in Phoenix, Arizona. He is currently pursuing a Master in Public Health degree from George Washington University with a focus in Humanitarian Health and Emergency Management.